IoT device manufacturers and service companies associated are now forced to (re-)evaluate securityduring all phases of their products’ life cycle.
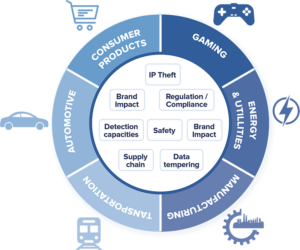
The massive proliferation of Internet-connected objects associated with an increasing number of attacks targeting them and increasing applicable regulations (Cyber Resilience Act, NIS 2, ETSI EN34343, IoT Consumer…) lead to highly consider security of devices and protection of intellectual property as major concerns for already deployed devices or future developments.
Talk to our experts
In the realm of Connected devices security, it is crucial to safeguard user privacy, protect data integrity, and ensure the reliability of systems.
Our experts focus on IoT device protection through comprehensive examinations of IoT architectures and communication protocols. By assessing vulnerabilities in embedded systems and scrutinizing device interactions, our experts ensure a resilient defence against evolving cyber threats. In essence, our methodology not only addresses current risks but also anticipate future challenges, reinforcing the trustworthiness of IoT ecosystems.
Partner with Quarkslab to harness our comprehensive suite of technical solutions and benefit from

Designing solutions providing the adequate safety level (secure boot, trust component, etc.)

Reducing the attack surface to maximize resiliency and reliability

Ensuring data authen-ticity, confidentiality, and integrity while facilitating key management

Enhancing safety by properly enabling and configuring advanced features

Attacking the connected device to verify that the safety measures are at the expected level
Collaborate with Quarkslab to fortify your security infrastructure, empowering your business to scale confidently and securely.
Our team of security experts is able to develop in-house tools (e.g such as TritonDSE, Binbloom…) to improve our security auditing services.
At every stage from the design to the release of the equipment: no recalls and remanufactoring, no crisis management to preserve your brand
Maintaining a red team to evaluate connected devices represents a significant cost and HR complexity given the lack of good technical profiles.
By meeting new standards or achieving CSPN certification, differentiate your solution from the competition
Resources