- How to measure the resistance of the protection
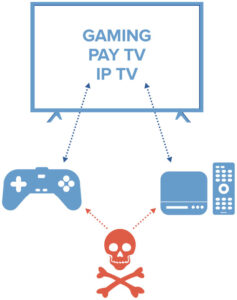
mechanisms of your gaming,
payTV or IP TV content broadcast solution? - How to understand the hacking techniques of a content broadcast service and its value chain to efficiently fight them?
- How to ensure that the business model of a video game or audiovisual content is protected?